Spot Dark Web Exposure Before It's Used Against You
Surface compromised credentials, customer data, and brand mentions across the dark web. AI-driven detection plus analyst validation means your team acts on real exposure, not noise.
Visibility Into What's Already Out There
Most dark web data is noise. Bolster AI cuts through it, surfacing only the exposures tied to your business.
Exposed Business Credentials
Credit Card Data
Phishing kits Targeting Your Brand
Breach data
Executive Protection
Threat actors actively monitor C-suite leaders and high-value employees, harvesting personal data to threaten extortion or damage reputations. Bolster AI surfaces that exposure first.
Compromised credentials
Executive and employee logins pulled from breach dumps and combolists, surfaced before attackers use them.
Doxxing & PII Exposure
Home addresses, phone numbers, and family details posted across forums and leak channels, weaponized for extortion, harassment, and reputation attacks.
Targeted Chatter
Executive and employee names appearing in criminal forums and Telegram channels, surfacing attacks while they’re still being planned.

The Sources We Cover
Most dark web data is noise. Bolster AI cuts through it, surfacing only the exposures tied to your business.
Dark Web Marketplaces
Criminal Forums
Telegram Channels
Ransomware Services
Anonymized networks
Paste Sites
Guides and Resources
Bolster your digital risk protection program and learn more about industry trends and managing threats.
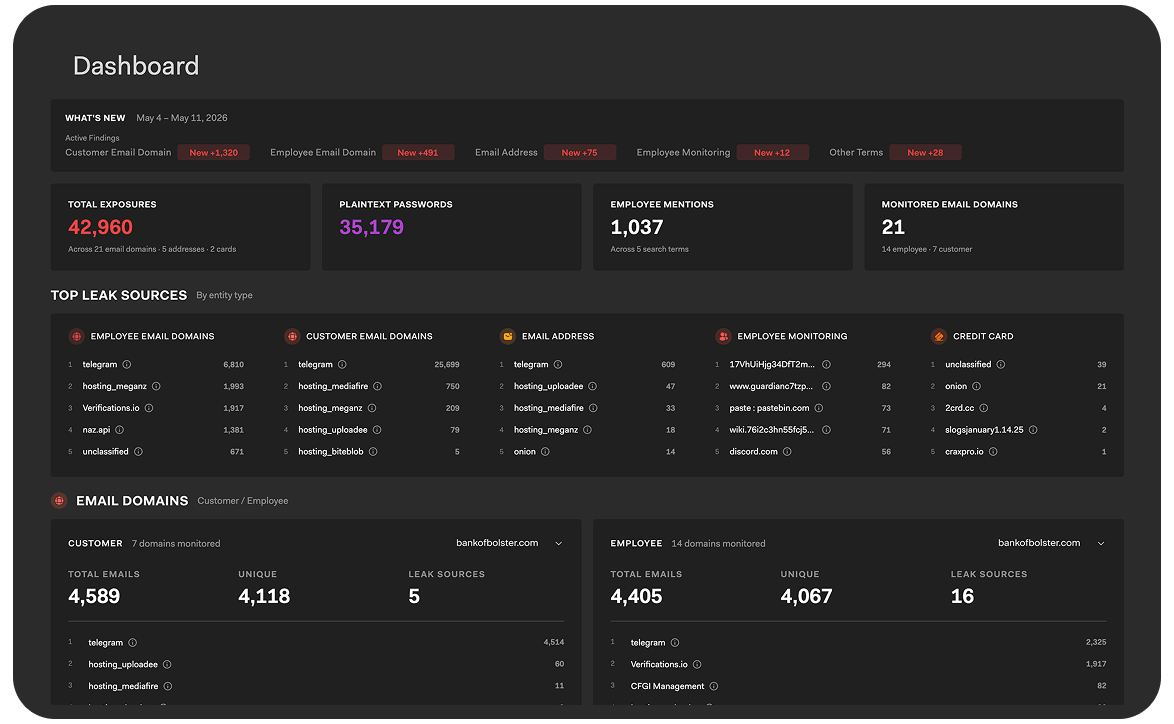
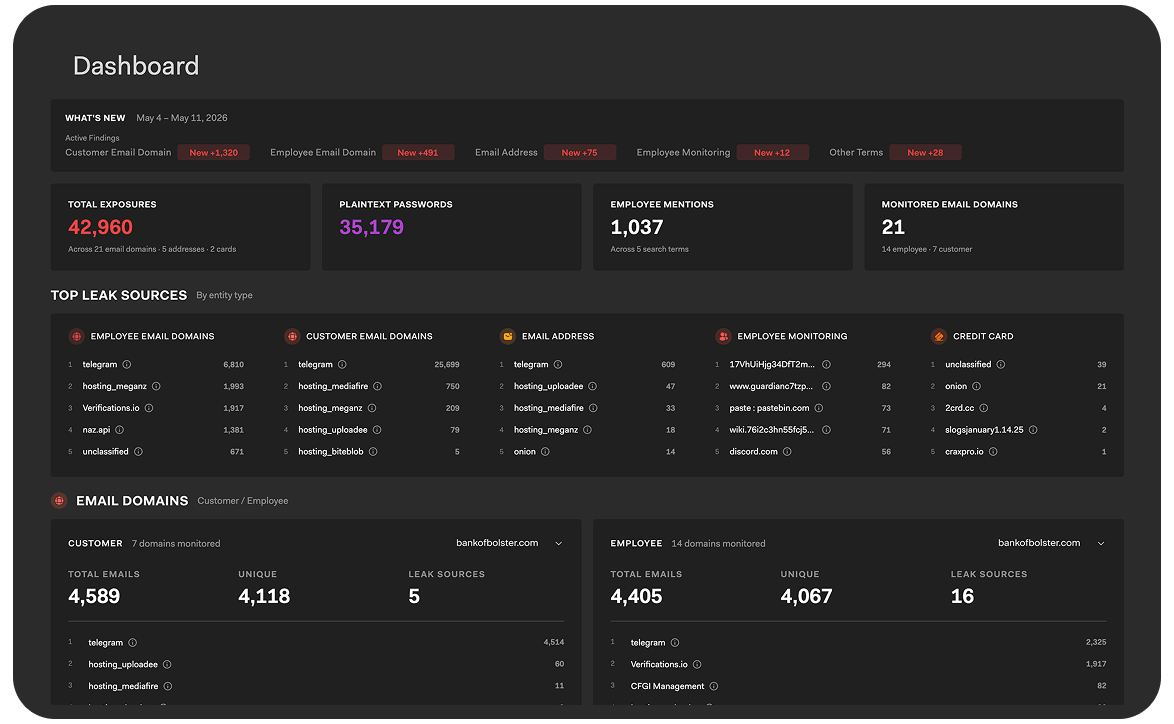
A Dark Web Dashboard Built Around Four Questions
The Bolster AI Dark Web dashboard gives your team a clear view of exposed credentials, leaked data, and emerging risks, without digging through raw breach data.
What’s New since The Last Scan?
See newly exposed credentials, employee mentions, and monitored assets as soon as they appear on the dark web. Quickly understand what changed, what matters, and where to investigate first.
How Big is My Exposure Overall?
Get an immediate view into your organization’s overall exposure, including compromised passwords, leaked employee data, monitored domains, and other high-risk findings, all prioritized for fast review.
Where is the Data Leaking From?
Identify the breach sources driving your exposure. Understand which leaks, combo lists, or marketplaces are contributing to risk so your team can respond faster and reduce repeat exposure.
Which Monitored Entities Are Most Affected?
Drill into the people, domains, emails, executives, or monitored entities seeing the highest exposure and focus remediation efforts where they matter most.
How Bolster AI Differs
Broad Visibility Across Dark Web
Monitor exposed data across criminal forums, marketplaces, Telegram channels, paste sites, and other hard-to-track sources from a single platform.
Signal, Not Endless Noise
Bolster AI combines automation with human validation to reduce false positives and help your team focus on exposures that actually matter.
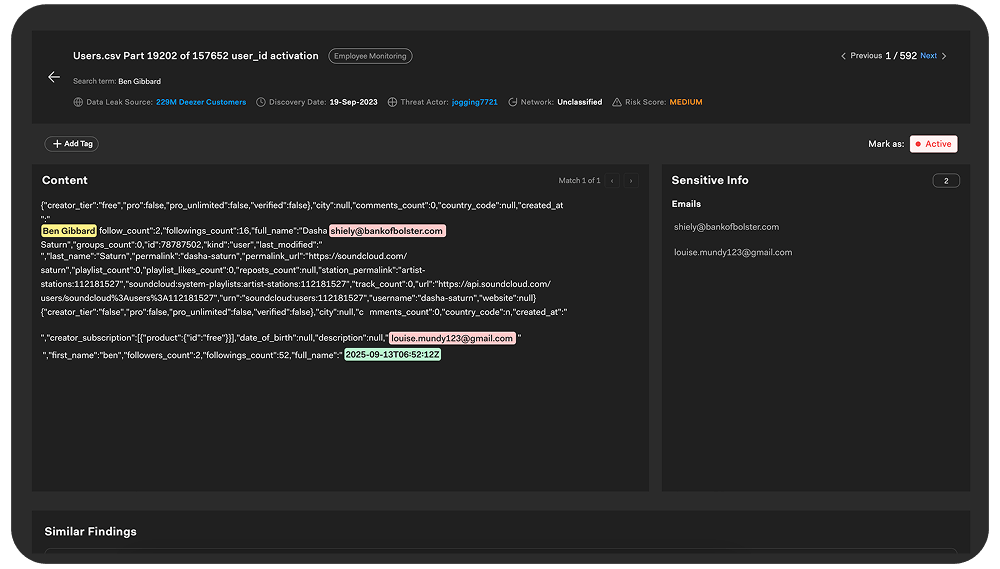
Faster Investigation & Response
Move from discovery to action quickly with guided remediation workflows, context-rich findings, and investigation paths built for security teams.
Exposure Prioritized By Risk
Not every leak carries the same risk. Bolster AI helps surface the findings most likely to impact your organization, executives, employees, and customers.
See Beyond the Leak Itself
Understand not just what was exposed, but where it’s spreading, who’s sharing it, and how threat activity evolves over time.
Dark Web Visibility, Before and After
With Bolster AI
A single dashboard ranks exposure, source, and entities
Plaintext credentials surface separately from totals
Correlation across entities happens automatically
Weekly scans catch exposure while it’s still fresh
Without Bolster AI
Security teams wade through raw feeds and lists
Severity stays buried in the noise
Cross-source correlation happens manually
Exposed credentials surface after they're already in use
McAfee Automates Customer-Reported Phishing Threats at Scale
See how McAfee partners with Bolster AI to triage thousands of phishing reports, take down threats faster, and reduce internal workload by more than 50%.



Ready to get started?
Explore what Bolster AI can do for you with a custom demo for your online business to understand existing online threats and how Bolster can take them down. Contact our sales team for pricing and packages today.
Frequently Asked Questions
What is the dark web?
The dark web is a hidden part of the internet not accessible through traditional search engines. It runs on anonymized networks like TOR and I2P, where threat actors trade stolen credentials, breach data, and attack tools under cover of anonymity and cryptocurrency-based transactions.
What is dark web monitoring?
Dark web monitoring is the continuous scanning of dark web sources for credentials, breach data, and threats targeting your business. Effective monitoring surfaces exposure quickly so security teams can respond before the data is used against them.
Why do businesses need dark web monitoring?
Stolen credentials, leaked data, and ransomware activity circulate on the dark web before the affected business is aware. Without monitoring, the first sign of compromise is often a customer report or an active fraud incident. Monitoring closes that gap.
What are stealer logs?
Stealer logs are records of credentials harvested from infected devices by infostealer malware. They typically circulate on dark web channels within hours of compromise and contain fresh passwords, often more dangerous than older breach data because the credentials are still active. Bolster AI Dark Web Monitoring scans the criminal forums, marketplaces, paste sites, and Telegram channels where this kind of data surfaces.
How does Bolster AI Dark Web Monitoring work?
Bolster AI uses machine learning and natural language processing to scan a broad range of dark web sources, then prioritizes findings in a customizable dashboard. Human analysts validate edge cases, so what reaches your team is accurate and actionable.
Does Bolster AI take data down from the dark web?
No. Engaging threat actors to remove data is unreliable, since there is no way to verify they have followed through, and most companies have policies against paying threat actors. Bolster AI focuses on what you can control: surfacing the exposure, categorizing the threat, and recommending mitigation steps. For example, if a credit card BIN is for sale on the dark web, Bolster AI surfaces it so your team can freeze accounts and reissue cards to affected customers.
What is an initial access broker?
An initial access broker is a threat actor who sells access to compromised corporate networks on dark web marketplaces. Buyers, often ransomware operators, use that access to deploy attacks. Listings typically include the company sector, revenue, and the level of access available, making them a high-signal indicator of imminent risk.
How do I know if my credentials are on the dark web?
Without active monitoring, you don’t. Once data is leaked, it spreads across multiple sources and cannot be fully removed. Continuous monitoring is the practical answer: it surfaces exposure as it appears so you can reset credentials, revoke sessions, and take action before attackers exploit the data.